Networking & Systems
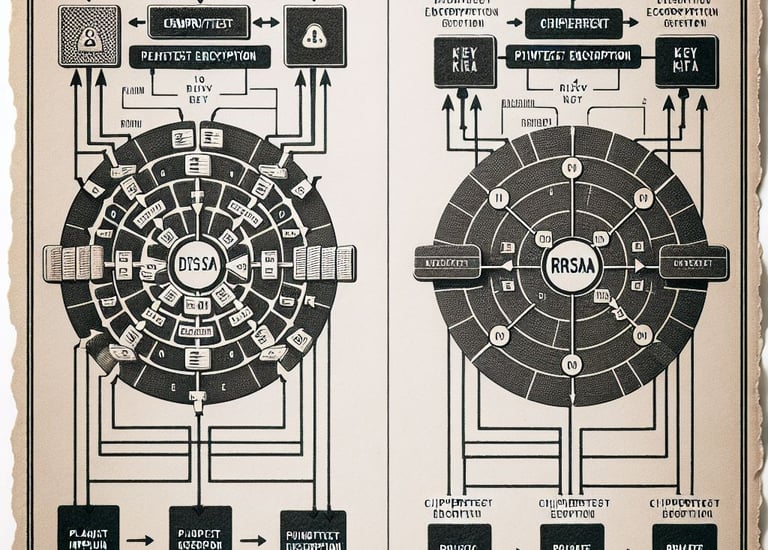
Analyzed and implemented DES and RSA cryptographic algorithms to understand public-key and symmetric-key data encryption standards.
Computer And Network Security
Cracking Wi-Fi password, This information is for educational purposes only, I am not responsible for its use.
Computer And Network Security
Explored how Internet of Things (IoT) devices interconnect to streamline business processes, optimize data flow, and drive operational efficiency. (Video)
Distributed Systems
Analyzed the core architectures of distributed computing, focusing on scalability, fault tolerance, and secure resource sharing across enterprise networks.(Video)
Analysis Of Algorithms
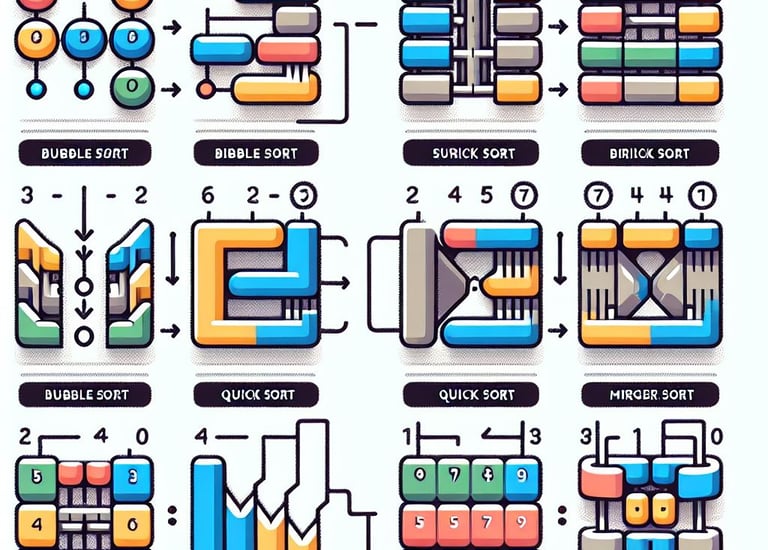
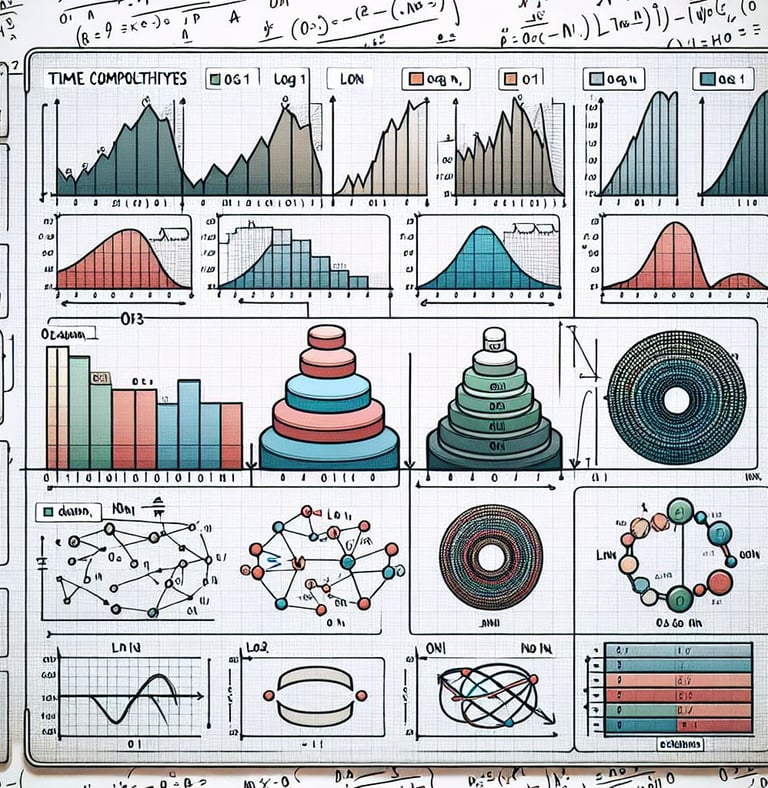
Benchmarked various sorting algorithms to analyze time complexity and computational efficiency for large data sets.
Analysis Of Algorithms
Designed algorithmic logic to efficiently traverse and search bidimensional grids, optimizing data retrieval processes.
Analysis Of Algorithms
Developed highly optimized algorithms focused on reducing execution time and improving overall software performance.
Analysis Of Algorithms
A deep dive into the QuickSort algorithm, demonstrating advanced problem-solving skills and mathematical optimization for efficient data processing. (Video)
Analysis Of Algorithms
Programmed and tested the QuickSort algorithm, demonstrating strong logical structure and efficient memory usage
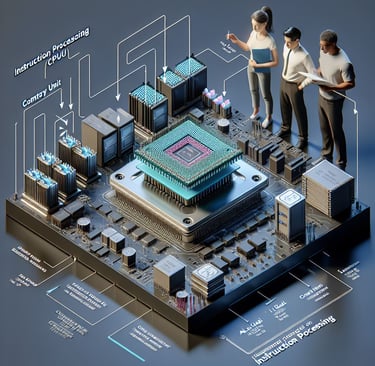
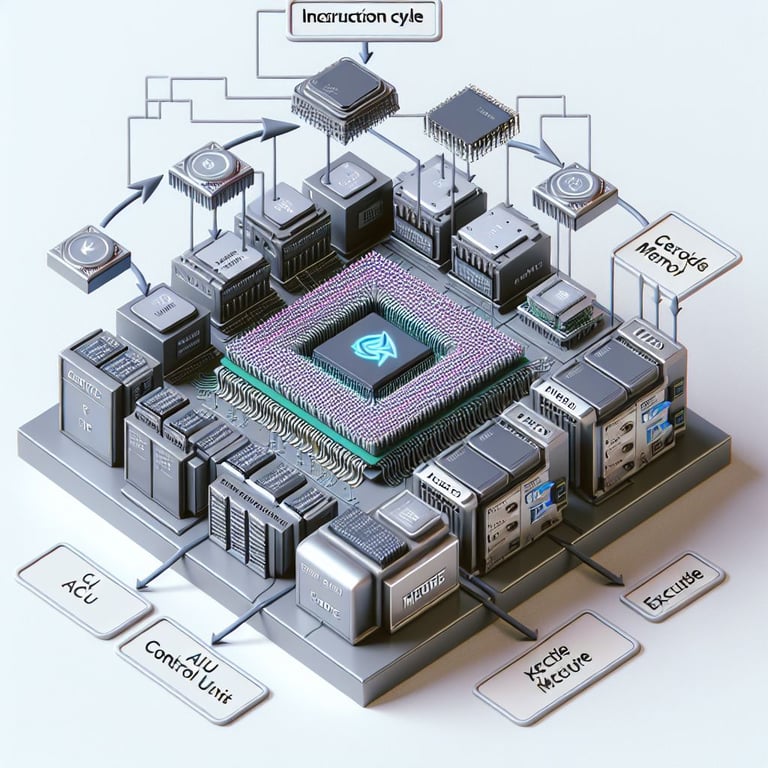
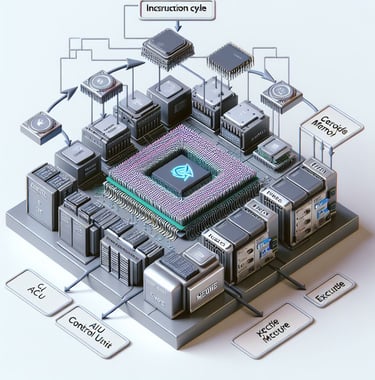
Computer System Architecture
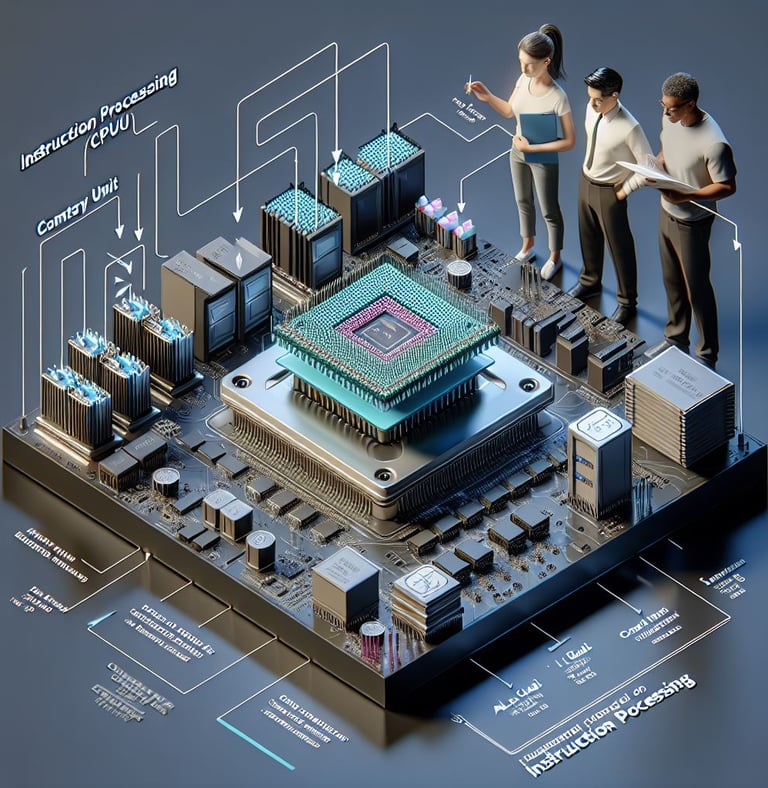
Mapped the complete instruction execution cycle to understand CPU processing at a hardware level and optimize code compilation.
Computer System Architecture
Encryption and Decryption on AES with OpenSSL
Computer System Architecture
Explored how Graphics Processing Units (GPUs) parallelize mathematical computations to accelerate blockchain verification and mining.
Wireless Security
Detailed breakdown of memory caching mechanisms and their critical role in reducing system latency and accelerating hardware performance.(Video)
Wireless Security
Demonstrated methods for identifying and mitigating rogue access points to prevent unauthorized network intrusion and data interception. This information is for educational purposes only, I am not responsible for its use.
Wireless Security
Comprehensive overview of wireless network vulnerabilities, cryptographic protocols, and best practices to secure enterprise Wi-Fi environments.(Video)
Multimedia & Web Development
Outlined best practices for integrating and optimizing multimedia content in web applications to ensure high performance and user engagement. (Video)
COMPUTER FORENSIC
Executed forensic methodologies to extract, preserve, and analyze digital evidence from mobile platforms for security investigations.
Computer Forensic
Examined digital forensic methodologies used to trace cyber incidents, recover compromised data, and strengthen incident response strategies.(Video)
Networking
Engineered the fundamental architecture and peer-to-peer networking logic required to build and deploy a functional cryptocurrency.
Practical demonstration of socket programming to enable secure, real-time bidirectional communication between client and server nodes. (Video)
Networking
Cybersecurity & Forensics
Architecture & Algorithms
Web Development
Cybersecurity & Encryption
Algorithms & Logic
Comparison of Sorting Algorithms
Architecture & Emerging Tech
Contact Us
Get in touch to explore innovative IT solutions for your business.
© 2026. All rights reserved.